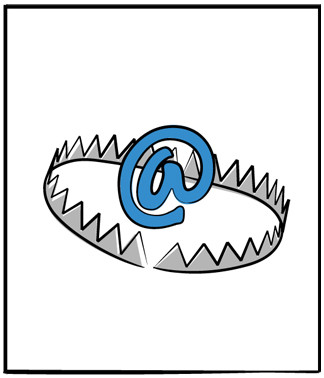
What is a spam trap? This one is important, so if you don’t know, find out.
Simply, spam traps—also known as honeypots—are valid email addresses which exist for the sole purpose of catching spammers at work.
And emailing spam traps is possibly the most serious offense an email marketer can commit. A single spam trap hidden in your list of emails will affect your deliverability and could even get your domain blacklisted with an ISP.
If a spam trap was created from a recycled email address, the ISP will report any message as a hard bounce. This will negatively affect your deliverability. However, DeBounce also uses this information to your benefit. Because our database monitors the trends of millions of contacts, we can predict the likelihood that an email will be returned as a hard bounce. We then isolate these addresses in real-time and offer you the opportunity to remove them from your list.
However, it’s important to remember that email validation is not a one-and-done solution nor is it a catch-all for spam traps. While DeBounce’s real-time email verification API or automated batch processing can certainly help to navigate around traps, it’s important that companies focus on organic address acquisition and regular list cleaning as well. Email verification will weed them out for you. The top services update their spam trap databases weekly. While no service can guarantee to identify 100% of spam traps, regular validation of your mailing list will keep you as protected as you can be.
DeBounce has no guarantee for finding all spam-traps on your email lists.
Procedures We Follow to Detect Spam-Traps
1. Cleaning by Crossing
The principle of this method is quite simple. As the name suggests, we will cross the data collected emails with that of a basic pitfalls address data. This method remains uncertain. It asks to have the sources of traps database. These sources are often random and slightly sour. And it must especially be sure to have a database containing addresses traps regularly updated. We find this unreliable method although it may serve as support.
2. Algorithmic Cleaning
This method is innovative, it goes beyond cleaning by crossing. For starters, the files will be analyzed and crossed with numerous files containing Black Lists of email. Then, a search engine with an artificial intelligence will scan your mail addresses to detect possible risks.
Some elements of an email address can generate a risk or spam-trap alert. An email address is divided into two parts: the recipient and the domain name. The process will move its parts scanner to check and generate alerts on various points:
- Wrong input or spelling of a domain name
- Anti-Spam email addresses
- Senders of exotic names: [email protected]
- Domain spam parking, cybersquatting ...
- Keywords suspects (@spam, bulkmail@, admin@, contact@, info@, etc.)
- DNS invalid, incorrect or misconfigured Mx
- Non-existent domain names: Mole Network
- Blakhole, unknown domain name
- Clickbots, email lists known to be bots
- Etc...





![Email Accessibility Guide [2024]](https://ik.imagekit.io/debounce/wp-content/uploads/2022/07/email-accessibility-guide-2-300x139.png)